The age of remote work has transformed the corporate landscape, providing companies with higher productivity and reduced staff turnover. However, while this major shift has brought many advantages, it has opened many opportunities for malicious individuals online.
Cybersecurity has become more crucial now than ever. As remote employees, you must be more vigilant about the threats you may encounter online.
We explore how to secure your remote working environment. Discover all the essential practices you can do to protect your personal and company data.
Learn the Latest Tools and Practices
Cybercrime breaches often occur because of a human problem, primarily from a lack of knowledge on detecting and fending off hacking attempts. Online users could haphazardly navigate the internet, from clicking questionable links to downloading malicious programs, risking precious company and personal data.
Learning about the different cybersecurity threats and the latest countermeasures is crucial to reducing the chances of attacks while working remotely. Understand all threats, from phishing to malware, and equip yourself with the best practices and tools to prevent them. That way, you add a layer of security to your devices, even without IT support in your home office.
It would also help to educate family members at home. Sharing your knowledge about cybersecurity threats will help protect your private network. You may be conducting the best practices or employing the right tools, but hackers could still reach you if anyone in your household gets compromised.
Install Robust Cybersecurity Software
Many antivirus programs provide countermeasures against different cyber attacks. Investing in one is crucial to remove all vulnerabilities in your devices that hackers could use to penetrate your data.
Various antivirus platforms are available for purchase today. Consider different factors to gauge the best fit when getting one for your device. First, you must determine if the program offers real-time prevention and quick infection removal whenever it detects an anomaly.
A quality antivirus program must also be easy to use. It must allow users to scan and remove any issues with a few clicks of a button. Aside from that, it must be compatible with different operating systems or any configurations.
Lastly, try getting a platform that offers more than detecting and eliminating issues. Other software provides services like password manager, leak monitoring, and virtual private networks (VPN). The good news is that you can try these programs for free before purchasing.
Use a VPN for Safer Online Connections
A VPN is a popular tool that allows online users to mask or encrypt their IP address and other online data transmitted from their devices. You can hide your data from hackers, internet service providers, and other online parties through a VPN.

This platform is helpful for remote workers who are always accessing public Wi-Fi networks at coffee shops or other similar establishments. Connecting to public Wi-Fi is risky because it’s not as secure as private networks. Some may allow hackers to access, monitor, and acquire various user data. Encrypting your connection with a VPN prevents such an attempt on your device whenever you work outside.
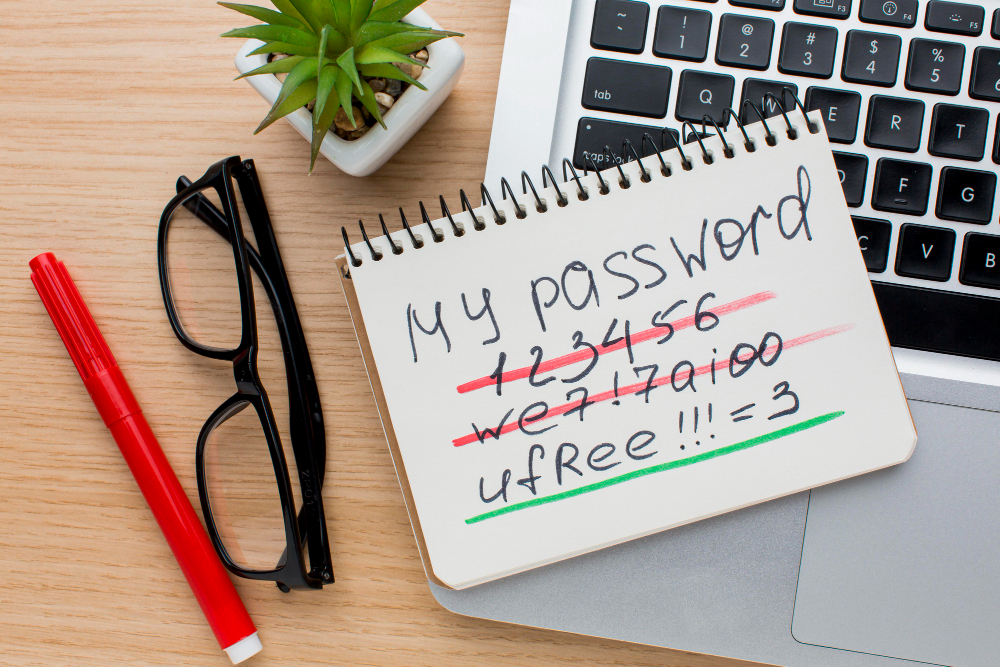
Generate Stronger Passwords
Weak passwords are one of the many human errors that hackers take advantage of when penetrating a device. Remember that passwords are your first defense in your cybersecurity countermeasures. That said, experts advise users to create a robust password combination that will be harder for hackers to guess.
Ideally, your passwords must never include personal information. These include names, birthdays, and phone numbers. You must also avoid using actual words because hackers can use programs that crack passwords by going through dictionaries. It must combine random letters, numbers, and symbols and be 12 to 16 characters long. Plus, it must be a mixture of uppercase and lowercase letters.
Never reuse your passwords across multiple devices and accounts. Doing so will put your data at risk of credential stuffing. Credential stuffing is a cyberattack where hackers use stolen user IDs and passwords to access different accounts illegally.
Ensure Your Programs Are up to Date
More often than not, software upgrades contain solutions to vulnerabilities found in their previous versions. Ignoring these updates could allow hackers to penetrate your devices through these programs. They can target these weaknesses to sneak malicious code that infects your computer and steals your data.
Most software companies practice automatic updates for their systems. They will likely notify you of any available upgrades to the program. However, checking for pending upgrades to your software and operating systems is still best. You should also do the same to your smart devices by visiting your app providers and looking for updates.
Practice Better Cybersecurity Measures
Going remote has many benefits to employees. However, to maximize those benefits, you must practice the best countermeasures against various cyber attacks to ensure a secure and seamless remote working experience. Protect your personal and company data by conducting the steps above.
ALSO READ: THE BENEFITS OF COMBINING AUTOMATION AND HUMAN EXPERTISE FOR CYBERSECURITY





