As hybrid and remote work become permanent fixtures of the Australian business landscape, secure connectivity has shifted from a technical nicety to an operational necessity. Today’s organisations rely on a mix of remote access technologies to protect data in transit, meet regulatory obligations, and keep distributed teams productive—without exposing internal systems to unnecessary risk.
Rather than depending on a single tool, modern secure connectivity strategies combine encrypted access, identity controls, and device-level protections to create a more resilient security posture for remote and hybrid workforces.
Why Secure Remote Connectivity Matters More Than Ever
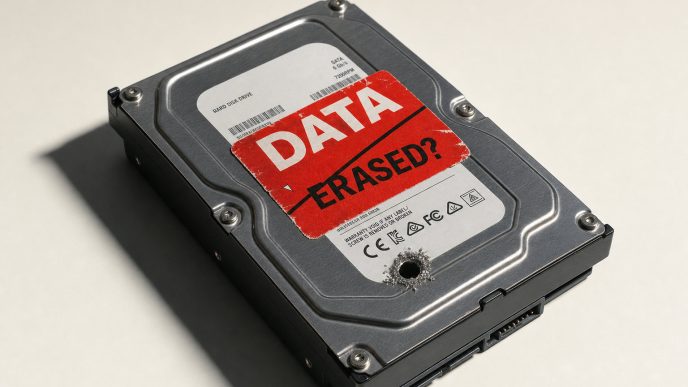
The threat environment facing Australian organisations continues to intensify. According to the ASD’s Annual Cyber Threat Report 2024–25, the average self-reported cost of cybercrime per business incident has risen 50% to $80,850, with small businesses reporting average losses of $56,600. These figures underscore a clear reality: remote access is now a primary attack surface.
Secure connectivity technologies help reduce this risk by protecting data as it moves across public and private networks, limiting unauthorised access, and ensuring employees can work safely from any location. For businesses operating across multiple offices—or supporting staff working from home, on the road, or overseas—secure remote access is no longer optional; it is baseline security hygiene.
Core Building Blocks of Secure Remote Access
Effective remote connectivity relies on multiple, complementary controls rather than a single solution. Common elements include encrypted network connections, strong user authentication, and visibility into the devices accessing business systems.
Encrypted access mechanisms protect data from interception, particularly when staff connect via home networks, shared workspaces, or public Wi-Fi. This may be delivered through technologies such as secure gateways or a small business VPN, which provides encrypted access without the complexity of larger enterprise deployments. Identity-based controls, such as multi-factor authentication, ensure that access decisions are tied to verified users rather than just network location.
Together, these controls significantly raise the barrier for attackers attempting to compromise accounts or intercept sensitive communications, while still allowing staff to work flexibly and efficiently.
Supporting Remote and Hybrid Teams at Scale
Implementing secure connectivity across a distributed workforce involves more than selecting a single technology. Businesses need solutions that support multiple device types, integrate with identity platforms, and allow centralised policy management as teams grow or change.
Just as important is user behaviour. Staff should understand when secure access tools must be used—particularly when handling client data, accessing internal systems, or working on untrusted networks. For many organisations, a centrally managed approach that combines identity controls with encrypted access—such as a small business VPN integrated into a broader security framework—provides a practical balance between protection and usability.
Clear policies around credential management, approved devices, and incident reporting help ensure that security measures are applied consistently rather than selectively.
Compliance, Privacy, and Regulatory Expectations
Australia’s privacy obligations have recently been strengthened. The Privacy and Other Legislation Amendment Act 2024 now requires organisations to implement both technical and organisational measures to protect personal information, with greater enforcement powers granted to the OAIC.
Secure remote connectivity plays a direct role in meeting these expectations. Encryption, access controls, and monitoring capabilities all support the principle of safeguarding personal and sensitive data, regardless of where employees are working from. As regulators increasingly focus on whether “reasonable steps” have been taken, remote access security should be viewed as a core component of an organisation’s compliance posture—not an IT afterthought.
A Practical Path Forward
Securing remote connectivity is no longer a problem businesses can defer. With threats rising and regulatory expectations tightening, organisations need a layered approach that balances security, usability, and scalability.
While tools such as a small business VPN remain an important part of this picture, they are most effective when combined with strong identity controls, device security, and clear internal policies. Taken together, these measures help protect people, data, and reputation—while enabling the flexible working models that modern Australian businesses now depend on.