Cisco today unveiled a host of new capabilities and services that give security professionals extensive intelligence and analysis on potential compromises and solutions to protect against, respond to and recover from attacks.
Cisco announces the addition of AMP Threat Grid to the Cisco Advanced Malware Protection (AMP) portfolio, which integrates innovation acquired through last year’s acquisition of ThreatGRID. This integration provides the latest malware threat intelligence and dynamic malware analysis capabilities, both on-premise and in the cloud, that strengthens Cisco AMP’s continuous analysis and zero-day detection capabilities. In addition, Cisco is introducing Incident Response Services that equip Kenyan organizations with teams of information security experts that leverage threat intelligence and best practices for readiness and response from network to endpoint to cloud.
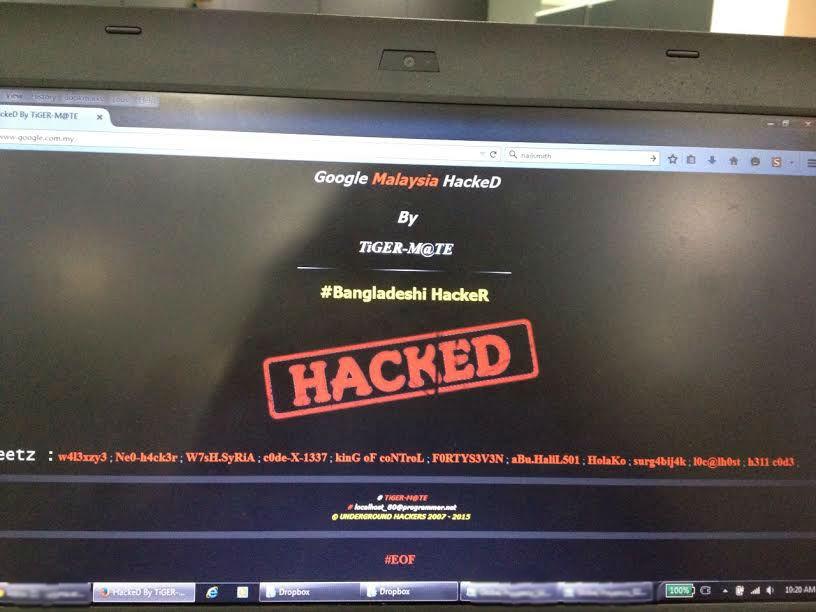
As dynamic as the modern threat landscape is, there are some constants; adversaries are committed to continually refining and developing new techniques that can evade detection and hide malicious activity. This is evident by the 250 percent increase in malvertising attacks as cited in the Cisco 2015 Annual Security Report. Additionally, the report continues to show that enterprises are in a persistent state of infection, showing 100 percent of networks analyzed had traffic going to websites hosting malware.
AMP Everywhere
New threat intelligence, dynamic malware analysis and retrospective security capabilities for Cisco AMP enhance protection across the attack continuum. AMP Threat Grid provides dynamic malware analytics and threat intelligence. AMP Threat Grid analytics engines provide security teams with breach detection against advanced malware, allowing them to quickly scope and recover from a breach by providing context-rich, actionable threat intelligence.
Unique to Cisco AMP, the solution continuously records and analyzes file activity at and after initial inspection. If a file exhibits malicious behavior after the fact, retrospective security rolls back the tape to see the origin of a potential threat, the behavior it exhibited, and provides built‐in response capabilities to contain and eliminate the threat.
Cisco Security Incident Response Services: Threat Protection Expertly Applied
There is a widening gap between the availability of expert security practitioners and the industry’s needs, as companies lack both funding and manpower to adequately protect assets and infrastructure. Chief Information Security Officers are increasingly looking to external experts for security guidance.
Leveraging threat intelligence from the Cisco Talos Security Intelligence and Research Group, AMP and the expertise of the Cisco Security Solutions (CSS) team, the Incident Response Services group works with organizations to identify the source of infection, where it entered the environment, and what data was compromised. It will support businesses in two areas:
- Cyber Attack Response: Every event is unique and Cisco Security Incident Response methodology provides expedience and allows for flexibility to continuously adjust to the dynamic threat landscape. Whether it’s an insider threat, distributed denial of service, advanced malware at the endpoints or customer data breach, the team guides an organization through identification, isolation and resolution using Assessment, Analysis and Data Mining; Forensic Image Analysis; Infected System Dynamic Instrumentation; Malware Reverse Engineering and Exploit Analysis and Re‐
- Cybersecurity Readiness: As businesses fall victim to increasingly targeted cyber-attacks and data breaches, they need external expertise to assess and promote security best practices as well as to protect corporate data and prepare for the inevitable data breach incident. Cisco Incident Response offerings spans infrastructure breach preparedness assessments, security operations readiness assessments, breach communications assessments among others.